Vulnerability of Microsoft Teams (GIF)
Remote cooperation and applications related thereto are becoming more and more searched for, not only by users but also by attackers trying to find new bugs and vulnerabilities in these products. Unfortunately, Microsoft Teams was no exception, and together with Zoom and others faced vulnerabilities that required a quick fix. The current version of Microsoft Teams no longer contains vulnerabilities, but it is interesting how it could have been allegedly exploited for several weeks.
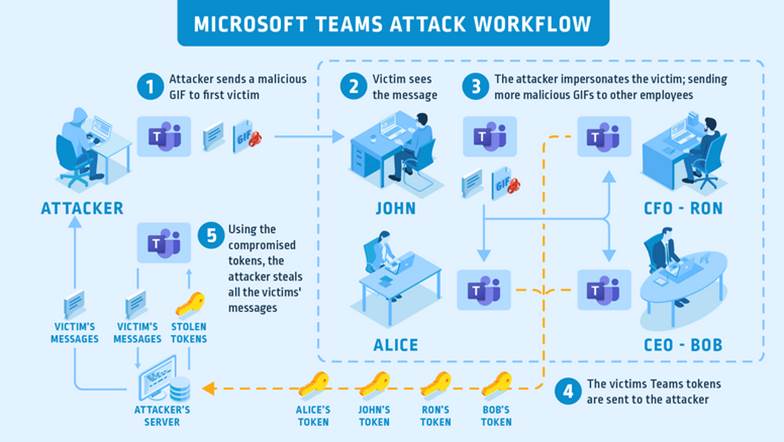
Figure 1: Attack vector for Microsoft Teams (Cyberark)
The vulnerability was revealed for the Microsoft Teams desktop application in the context of the workflow by redirecting traffic outside the Microsoft service and obtaining user access tokens. Ultimately, an inconspicuous GIF image could be sent to the user, which allowed the attacker to steal access and easily spread the infection internally under the user's identity. The overall vulnerability analysis is explained in detail, for example, on the Cyberark website. .
The services for communication between users have been and will be the target of attacks. Whether we are users or administrators, we have to take this fact into consideration and be careful. Microsoft Teams offers a large number of policies and settings that can help you reduce potential attack vectors or information leaks. You can consider using conditional access, allowing external communication only for the selected domains, disabling e-mail communication to specific channels, or enabling integration only for approved applications or disabling some external storages. Passive protection in the form of customized login screens and completed user profiles may also help identify fake information. Defined principles for communication, continuous user training and controlled simulations of attacks are other elements that increase data and user protection, so it is ideal to approach it comprehensively with respect to the effective use of the service and especially proactively, so that we are surprised by the creativity of attacks as little as possible.
Share on social media